Welcome to IT Monteur's Firewall Firm, India's No1 Managed Enterprise Network Security Firewall Support Provider Company in India
Best Firewalls for Small Business
Security must be integral, not an afterthought. There is no business that is 100% safe from cyber threats in today’s world. Cybersecurity should be a constant concern for businesses of all sizes. From the smallest family-owned store to the biggest multi-national conglomerates
Out of the box all-in-one security for small businesses
Enterprise grade network security, highly integrated, and easy to manage Firewalls at low Price in India
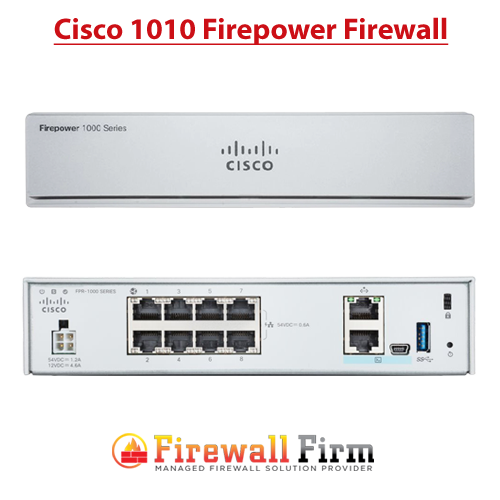
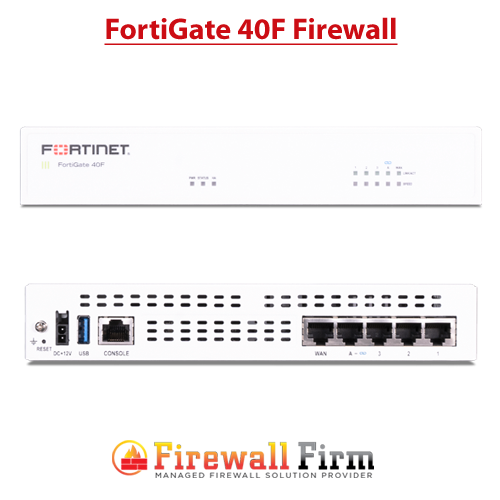
Top Selling Firewall Brands
Browse by Popular Category
Popular Category
Juniper Firewall Support , Cisco Firewall Support , Check Point Firewall Support , Palo Alto Firewall Support , FortiGate Firewall Support , Forcepoint Firewall Support , Sophos Firewall Support , WatchGuard Firewall Support , Baracuda Firewall Support , SonicWall Firewall Support , Gajshield Firewall Support , Seqrite Firewall Support , Firewall, Hardware Firewall, Software Firewall, Firewall India, Firewall, Network Firewall, Firewall Support, Firewall Monitoring, Firewall VPN, WAF Website Firewall, Firewall Security, Firewall India, Firewalls Provider in India
Security must be integral, not an afterthought.
40% of all cyber-attacks target businesses with fewer than 500 employees!, More than 40% of SMBs don’t have an adequate IT security budget! , SMBs on average lose $188,242 to a cyber attack and almost 66% of victimized companies are forced out of business within six months of being attacked. , Only 26% of small and midsize businesses were confident their firm has enough in-house expertise for a strong security posture , Despite the threat that data loss poses to SMBs, 70% thought their companies would have difficulty detecting a breach , Did you know the average breach goes undetected for 229 days?
Business Security Facts:
- You may be attacked, even though you’re small
- In fact, small businesses are attacked more than enterprises due to their lower security budgets and expertise, both of which equate to greater vulnerability.
- Cyber criminals gain access to larger corporations through small business networks.
- Security must be integral, not an afterthought.
- UTM (Unified Threat Management) is no longer enough.
- Wired & Wireless need common security policy.
Partnering with IT Monteur's Firewall Firm means:
- Installation and integration of firewall into the network
- 24/7 Protection, Monitoring and Threat Response of all access points to your network, offering complete security from outside threats
- Endpoint Security anti-virus protection safeguards your network from viruses, worms, and other malicious code threats
- Spam protection through message and e-mail filtering
- Dedicated Security Team
- Onsite support as needed
- Integrated Security with Business Focus
Software Firewalls
Free and Open Source Linux Network UTM Software Firewalls
All major Linux distros come with a software firewall built into them, since it is part of the Linux kernel itself. Linux based open source firewall that transforms your standard PC into a committed firewall and Internet server/gateway. Any user can configure their system firewall to get started with securing network traffic, but there are many alternatives to the default which will extend or simplify the functionality. Firewall Firm Provides Linux Firewall Setup, Configuration and Support start with for just $100 Per Month.
 Firewall Support Company in India All type of Firewalls Support Provider Company in India
Firewall Support Company in India All type of Firewalls Support Provider Company in India